Computer Files Encryption
Description
- Describe the five basic attacks on authentication systems.
- Outline the symmetric encryption process and explain the components involved in the process.
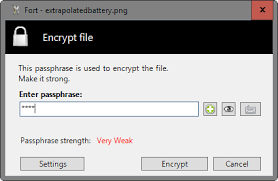
- Summarize the different situations in which people use file encryption software.
- Describe the different categories of asymmetric encryption algorithms and how they are used in practice.
Your assignment must follow these formatting requirements:
- Be typed, double spaced, using Times New Roman font (size 12), with one-inch margins on all sides; citations and references must follow APA or school-specific format. Check with your professor for any additional instructions.
- Include a cover page containing the title of the assignment, the student’s name, the professor’s name, the course title, and the date. The cover page and the reference page are not included in the required assignment page length.
We can write this or a similar paper for you! Simply fill the order form!




