Energy efficient computing, distributed mobile trusted computing & clouds, crowd sourcing and computing
Order Instructions:
your project should have an abstract, an introduction, a body of paper (literature review , previous work done bi others, technical and economical analysis, application and services, etc….) and your own contribution and engineering/technical opinion with a conclusion and of course a list of your references numbered as they are used in your write up. I use software to check the originality of your work. you will get zero if you just cut and paste form other sources. It is okay to use all types of resources (magazine, journals, internet, books, articles…) with proper citation
Topic: Energy efficient computing, distributed mobile trusted computing & clouds, crowd sourcing and computing
SAMPLE ANSWER
Energy efficient computing
Abstract
Efficient energy computing also known as green computing initiates the maximization and use of computing reserves with the aim of lessening the consumption of energy among other scarce resources. With the proliferation of an increasing powerful mobile devices, applications have been developed that can enable a user to collaborate through a mobile cloud with the aim of providing pervasive services such as; computing, data collection, and processing through efficient energy systems (Cătinean, & Cândea, 2013). Mobile users also have the advantage of taking over the outsourced tasks through the mobile cloud and crowd outsourcing that emerges as a service paradigm. By leveraging the capacity of a mobile device that integrates the intelligence of human beings and machine computation, the mobile crowd gives the ability to revolutionize the approaches involved in the processing and collection of data.
Introduction
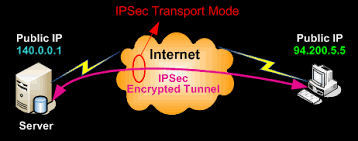
The genesis of the mobile devices and mobile computing has turned out to be an irresistible trend in the IT technology sector. With this, it is significant to mention that the mobile devices face some challenges and limitations including; memory, energy, and computation. In order to overcome these constraints, the mobile cloud computing approaches have proved to be the solution in enabling the mobile device users consumes a varied cloud resource through a wireless network (Cătinean, & Cândea, 2013).
This clouding computing method can, therefore, improve the computational ability through an energy efficient mobile device by offloading the computational tasks into the cloud services (Cătinean, & Cândea, 2013). The current and new-fashioned mobile devices have been embedded with versatile sensors that provide a novel paradigm with the capacity to collect a wider array of data about the society, the environment, and other important aspects. The intent of this exposition is to analyze the elements of an energy efficient computing, distributed mobile trusted computing and clouds, crowd sourcing and computing through a review of the literature.
Energy Efficient Computing, Distributed Mobile Trusted Computing & Clouds, Crowd Sourcing and Computing
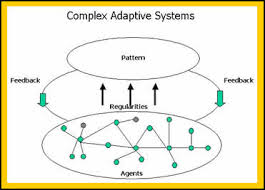
Through the empowered efforts and capabilities, mobile devices have shifted today from just the ordinary service providers that offer and make communication easier into a new service model that incorporates the elements of mobile cloud computing (Qi, Jianxin, & Yufei, 2014). The emergence of this technology and service model has led to the connection of mobile devices with each other through wireless networks, a factor that has resulted in the formation of a powerful mobile cloud that provides a persuasive approach to data collection, processing and computing through efficient energy consumption. It is important to mention that the evolution of the mobile cloud has given the mobile crowd sourcing a feasible solution for solving problems on a large scale. The literature review segment provides an overview into how these elements function.
Literature Review
The mobile crowd sourcing is a commercial electronic service in which the mobile users within a mobile cloud can sell their services and resources for service consumers (Qi, et. al). Through an outstanding task of the mobile cloud, a cost, and energy efficient pervasive cloud service is possible to attain through the use of massive numbers of mobile users working together in a distributive manner. The central idea behind a mobile crowd sourcing structure includes the involvement of a variety of applications that are differently utilized in a business model.
For instance, the author of this material gives an analogy of an Open Street Map that depicts a crowded map of the world that was developed by worldwide mobile users through the use of their knowledge, some donated sources and a GPS trajectory (Qi, et. al). The development of this application clearly indicates the fact that this mobile crowd sourcing has the capacity to revolutionize the traditional data collection and processing methods. I as much as the computing paradigm seems promising and poses a tremendous advantage, the mobile crowding sourcing is in its infancy stages since it is facing numerous challenges.
This approach is varied from the traditional cloud computing method that only relies on the internet connection since through the crowd sourcing; it is able to access a pervasive cloud service for both the local and online terminals (Qi, et. al). According to the author of this material, the main difference between the two mobile crowd sourcing approaches is the fact that all these models gives an interconnected mobile user the potential to be a service provider through an internet-based mobile crowd sourcing, while the other approach only allows mobile users within a specified vicinity to provide cloud services through a local-based mobile crowd sourcing service. In order to achieve the end-results of these elements, there are essential components of cellular crowd sourcing;
Service Consumers;
The service consumers, in this case, refers to the local and online users who from time to time require cloud services through a mobile crowd sourcing system and who utilize the cloud services by sourcing out tasks to mobile users.
Mobile Users;
Mobile users with the enablement of their mobile devices can perform a mobile cloud by providing cloud services to the online service consumers through a cellular Wi-Fi network or to the local consumers through a process where communication is made to the local servers by using Bluetooth and NFC techniques (Qi, et. al). In the event that a mobile user engages in an outsourced task that incorporates the local computing mobile cloud approach to executing the tasks required.
Centralized Servers;
A centralized server remains a mobile crowd sourcing avenue for the internet-based service consumers in which the crowd sourcing information is stored such as historical service records, users, and profiles that are used for service evaluation and task outsourcing (Qi, et. al). Centralized servers have the ability to provide a trusted service for task publishing in which tasks are allocated, reported, collected, and the feedback processing for the internet-connected mobile users and consumers.
Local Servers;
The local servers have the capacity to provide a local crowd sourcing service that involves an outsourced task broadcasting the result in a task result aggregation for the service ad mobile consumers within particular vicinity (Qi, et. al). The local servers are in many cases equipped with a dedicated mobile gateway that is tasked with the dissemination of functions and information to the neighboring mobile users and, in the long run, collects user results. However, a local server can only be deployed for commercial reasons and remains not trusted by the mobile users.
Previous Work Done By Others
Over a period now, many mobile devices have turned out to be the sensor and information hubs in our day to day activities. Through the integration of mobile computing and crowd sourcing approach, many applications have today emerged that have achieved efficiency in energy, cost-effective data computation, collection, and the processing services (Qi, et. al). The mobile crowd computing model is used to supply data computations and tasks to mobile consumers who can locally execute a task and offload them to a cloud server based on an individual data and computation resource.
The author states that human interventions have also played a significant role in mobile crowd computing since their intelligence has helped in the handling of tasks that are only suitable for human evaluation that the computation of a machine. These functions include image annotation, sentimental analysis, and entity resolution (Qi, et. al). An instance of this is given of Honeybee, which is a local-based mobile crowd computing application that enables users to detect their faces through a photographic task and can be carried out through a mobile device. The mobile users are required to use their devices to run face detection algorithms through photos blended with an individual’s evaluation.
Technical and Economical Analysis
It is significant to mention that the technicality of these IT technologies remains the primary challenge of security as one of the major concerns for the cloud service consumers, while at the back of everything, a mobile crowd sourcing is meant to originate from an assumption and perception that users should honestly provide accurate results. This, therefore, remains a significant challenge to the users since some malicious mobile users have developed mechanisms of misbehaving to undermine the crowd sourcing.
These malicious users have the capacity to fabricate computations or maliciously suspending an ongoing process. It is, however, crucial to realize that there are several approaches that are being tried with the aim of mitigating the impacts of malice in the task reports and to identify the irrational users (Shiraz, & Gani, 2014). Recently, a robust trajectory estimation approach geared towards alleviating the negative influences of malice in a crowd sourced user trajectory to identify fraudulent users. In relation to the economics of these technologies it is important that responsibility is directed towards the environment, a factor that is emerging for corporate IT entities. With the increasing pressure on efficient energy because of its conservative nature, there are emerging technologies geared towards regulating the consumption
Application and Services
The crowd sourcing approach has assisted in big data application. According to my opinion, there are contributions that can be engineered to enhance the mobile trusted computing & clouds, crowd sourcing and computing technologies. This includes an approach that will help this technology by integrating the mobile crowd sourcing with the big data analytics (Shiraz, & Gani, 2014). This application can be beneficial since it would enable Smartphone user’s book their train seats in advance based upon the mobility pattern model and the contributions of a mobile data user.
It is however important to note that jelling the mobile crowd sourcing model and the big data analytic can be challenging since the methods of data collection may prove and turn out to be huge on a mobile device, a factor that constrains the data velocity, and volume. Privacy should also be a measure to include in the development of these systems.
Conclusion
The advent of an increasing powerful mobile devices applications have been developed that can enable a user to collaborate through a mobile cloud with the aim of providing pervasive services such as; computing, data collection, and processing through an energy efficient system (Shiraz, & Gani, 2014). These systems have made it easier for users to use the clouding computing methods to, therefore, improve the computational ability through energy efficient mobile devices. The evolution of these technologies has therefore seen several inventions that have impacted the society today.
References
Cătinean, I., & Cândea, D. (2013). Characteristics of the Cloud Computing Model as a Disruptive Innovation. Review of International Comparative Management / Revista De Management Comparat International, 14(5), 783-803.
Qi, Q., Jianxin, L., & Yufei, C. (2014). Cloud service-aware location update in mobile cloud computing. IET Communications, 8(8), 1417-1424.
We can write this or a similar paper for you! Simply fill the order form!